Free Tools
The following free tools are provided by others and ourselves. If you would like to provide and/or donate the tools to us, please let us know.
Fraudfox
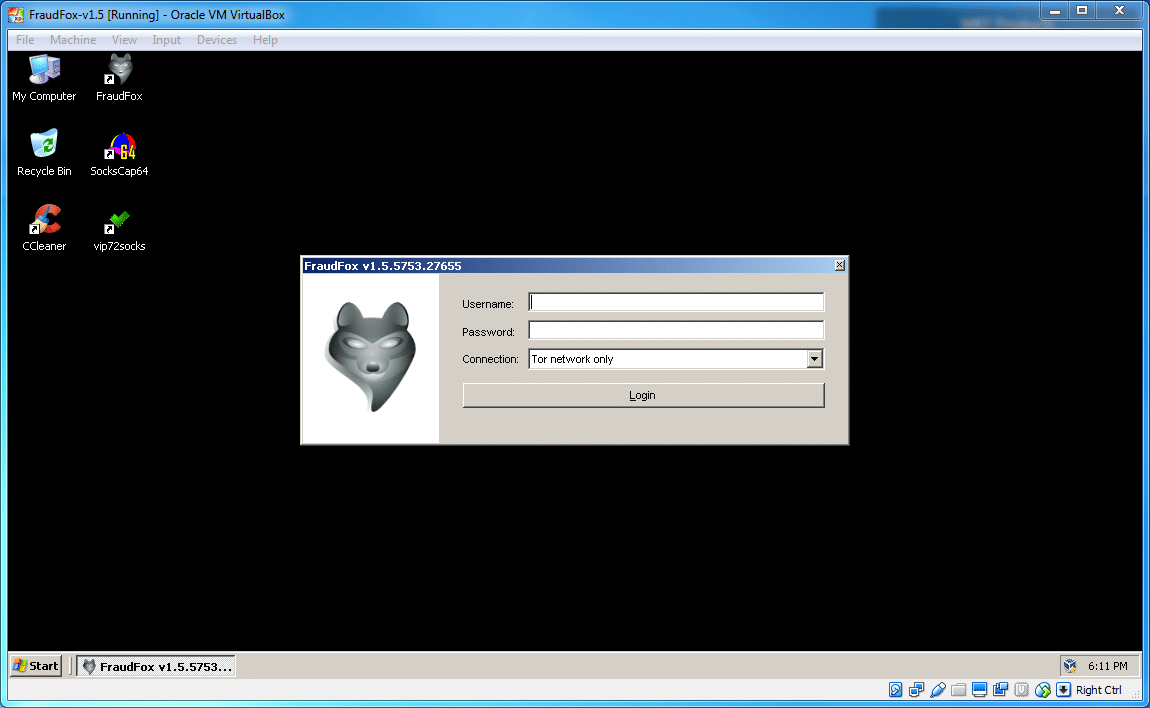
FraudFox is the all-in-one tool for user-agent and device spoofing and perhaps the most advanced and fully detailed virtual machine (VM) on its class ever created. For instance you can use VMWare on a Mac laptop and run it up so that you have a Windows desktop running inside of your Mac environment – giving you access to use programs and features that only Windows employs.
Antidetect
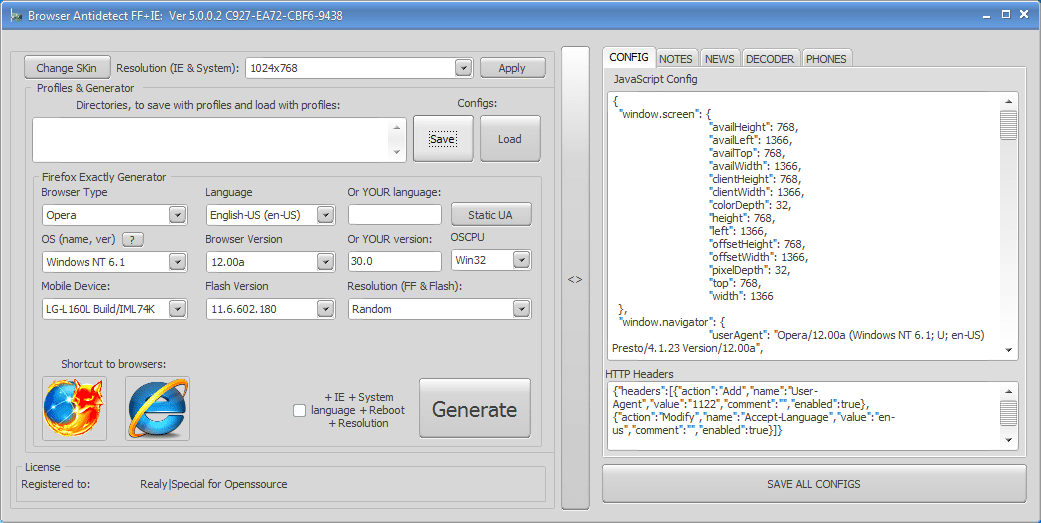
Carders are constantly looking for a new ways to avoid banks and e-commerce fraud detection systems. These security solutions are mostly relying on browser fingerprints, which is the data left by a computing device while interacting in the field of analyzing and comparing these data. AntiDetect Browser is one of the most prominent tools allowing you create a unique fingerprint to spoof the fraud detection system.
Credit Card Checker

Credit Card Checker tool is designed to check the validity of Credit Card / Debit Card Number and check the (BIN) base on updated database. The tool support all major Credit Card & Debit Cards brands such as as VISA, MasterCard, American Express, Diner's Club, JCB & Voyager. Currently, there are more than 300,000 unique BIN in our database.
Atomic Email Hunter
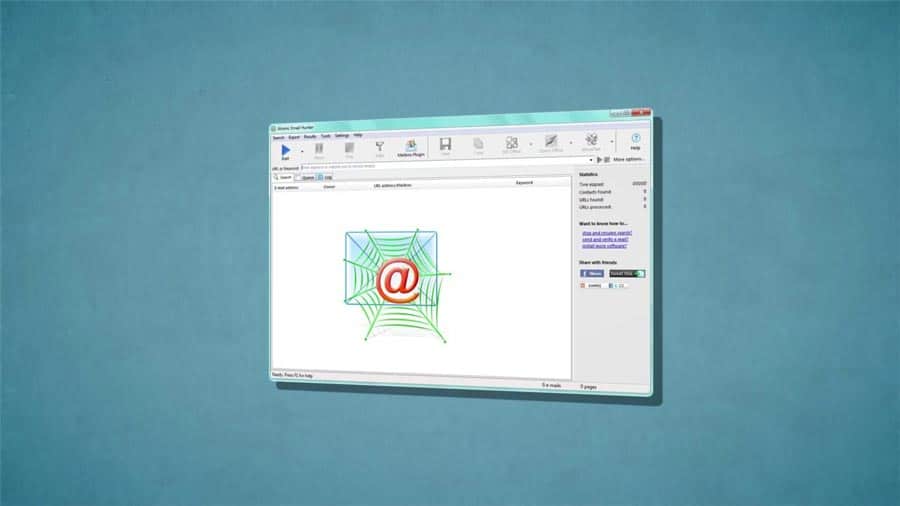
Atomic Email Hunter is a powerful tool that extracts and collects email addresses with usernames from webpages. It is a very flexible online email extractor designed to extract email addresses from websites and search engines. It's easy to use. In most cases, all that is required to get results is to enter a valid URL or type several keywords in the search bar. That's all that has to be done to get going with the tool - email search literally starts in a matter of seconds. Just enter atomic email hunter register key and start your work.
VMWare Workstation
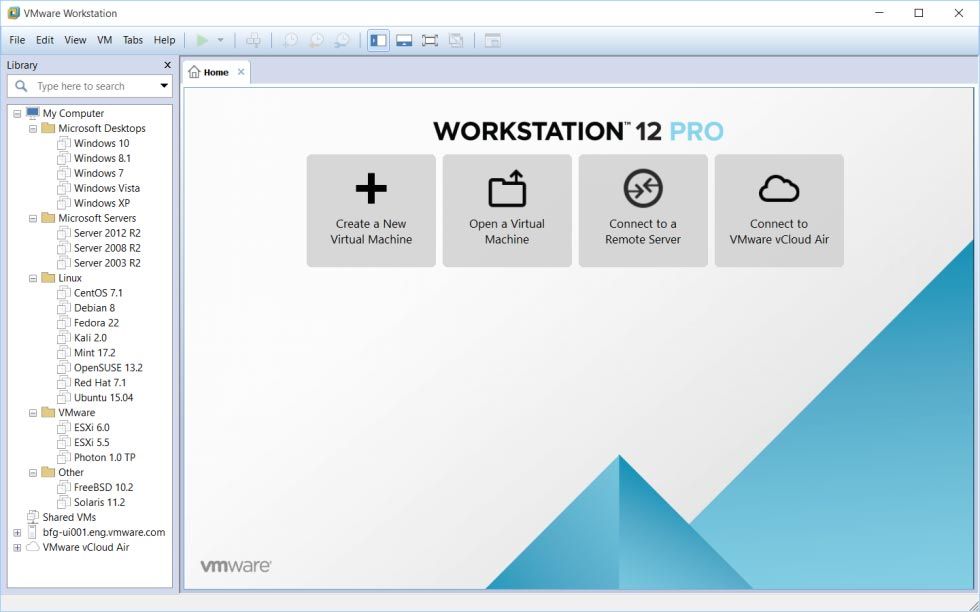
VMware Workstation Pro lets you run multiple operating systems as virtual machines (including Windows VMs) on a single windows or Linux PC.
Proxifier
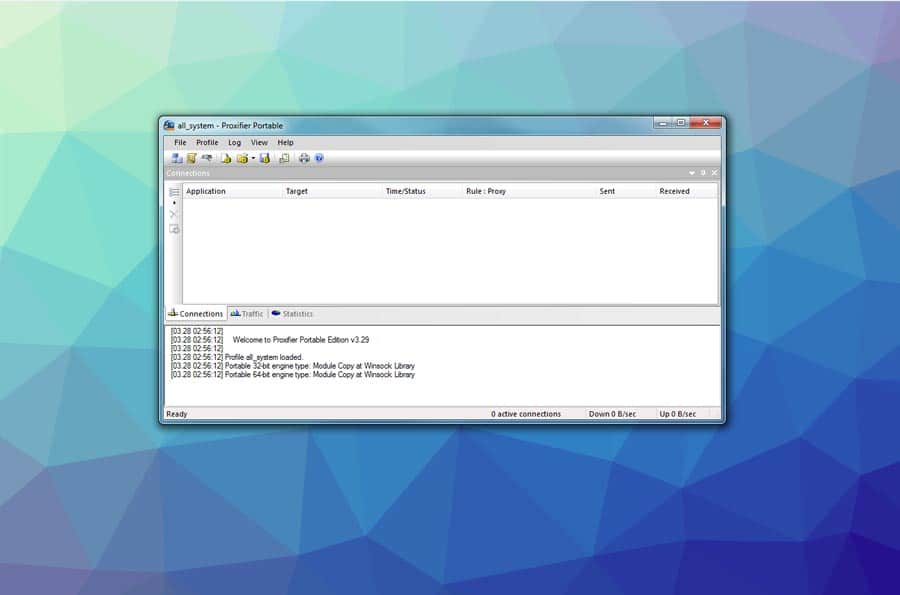
Proxifier is the the most advanced proxy client. It allows network applications that do not support working through proxy servers to operate through a SOCKS or HTTPS proxy and chains.



